- June 1, 2026 11:01 am
Latest Post
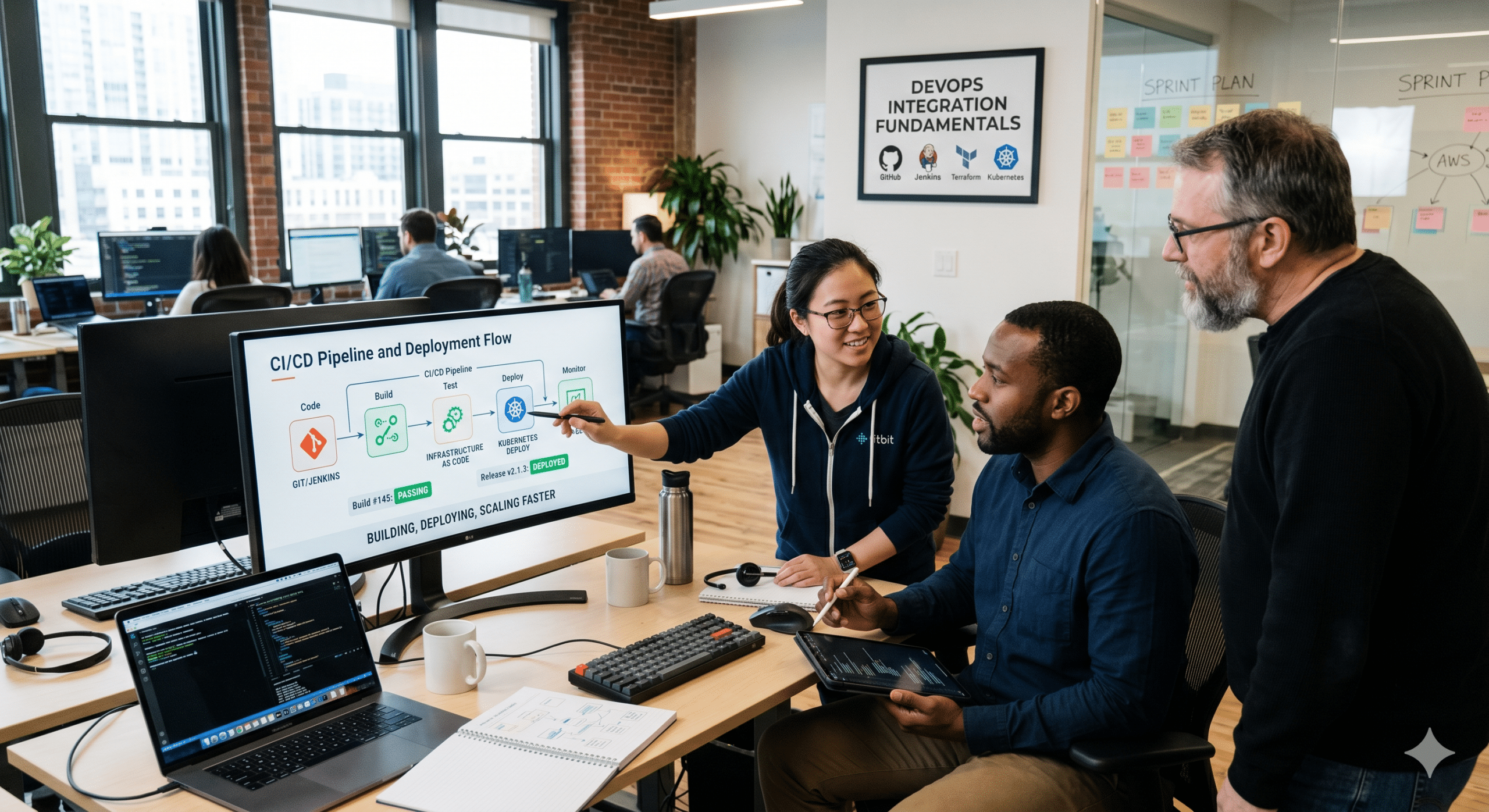
DevOps Integration Fundamentals: How Modern Teams Build, Deploy, and Scale Software Faster
The way software is built and delivered has changed dramatically over the past decade. Businesses no longer release major updates once or twice a year. Today, customers expect applications to…
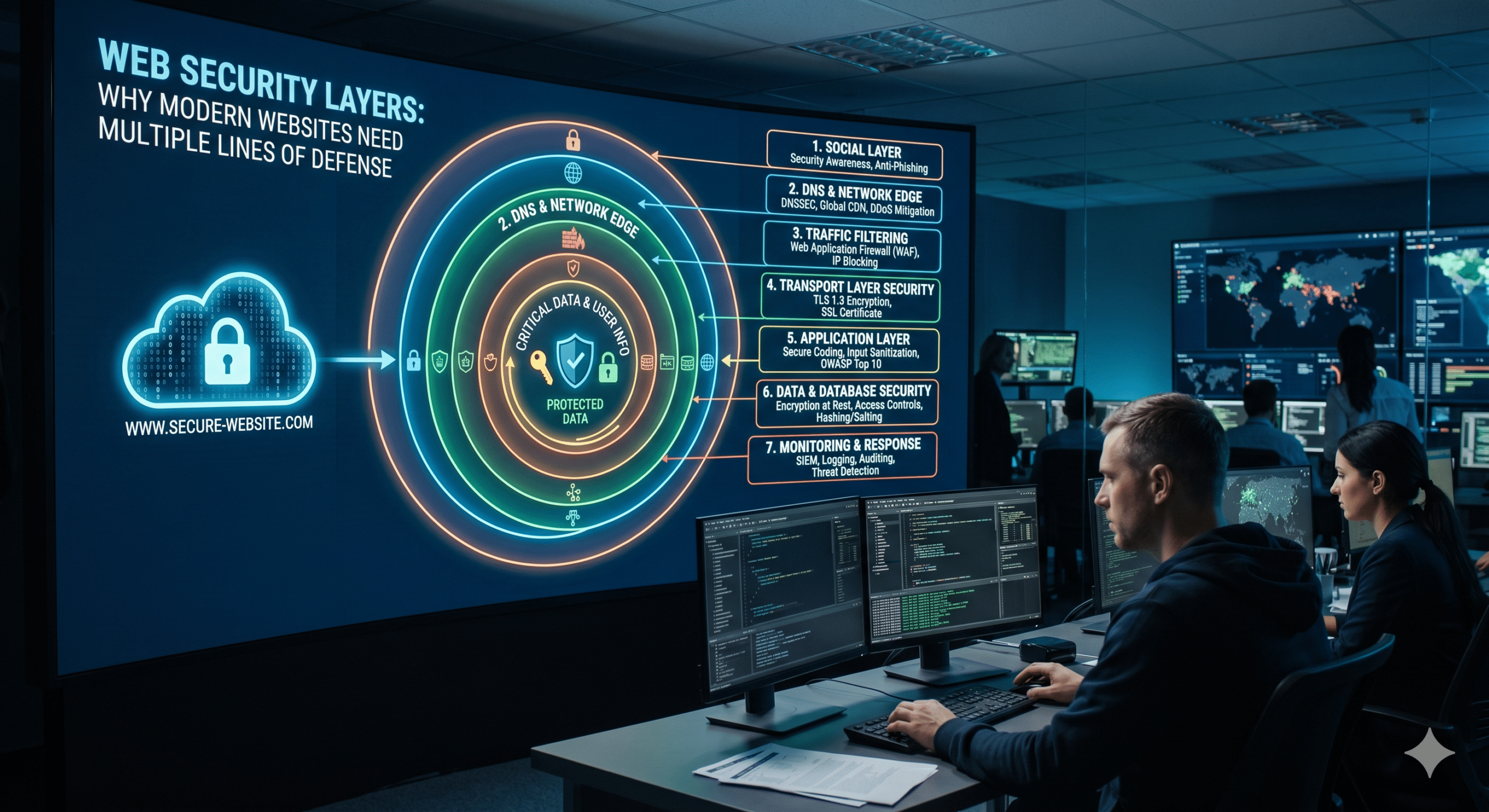
Web Security Layers: Why Modern Websites Need Multiple Lines of Defense Against Cyber Threats
In today’s digital world, websites face more threats than ever before. Cybercriminals are constantly looking for weaknesses they can exploit to steal data, disrupt services, spread malware, or gain unauthorized…
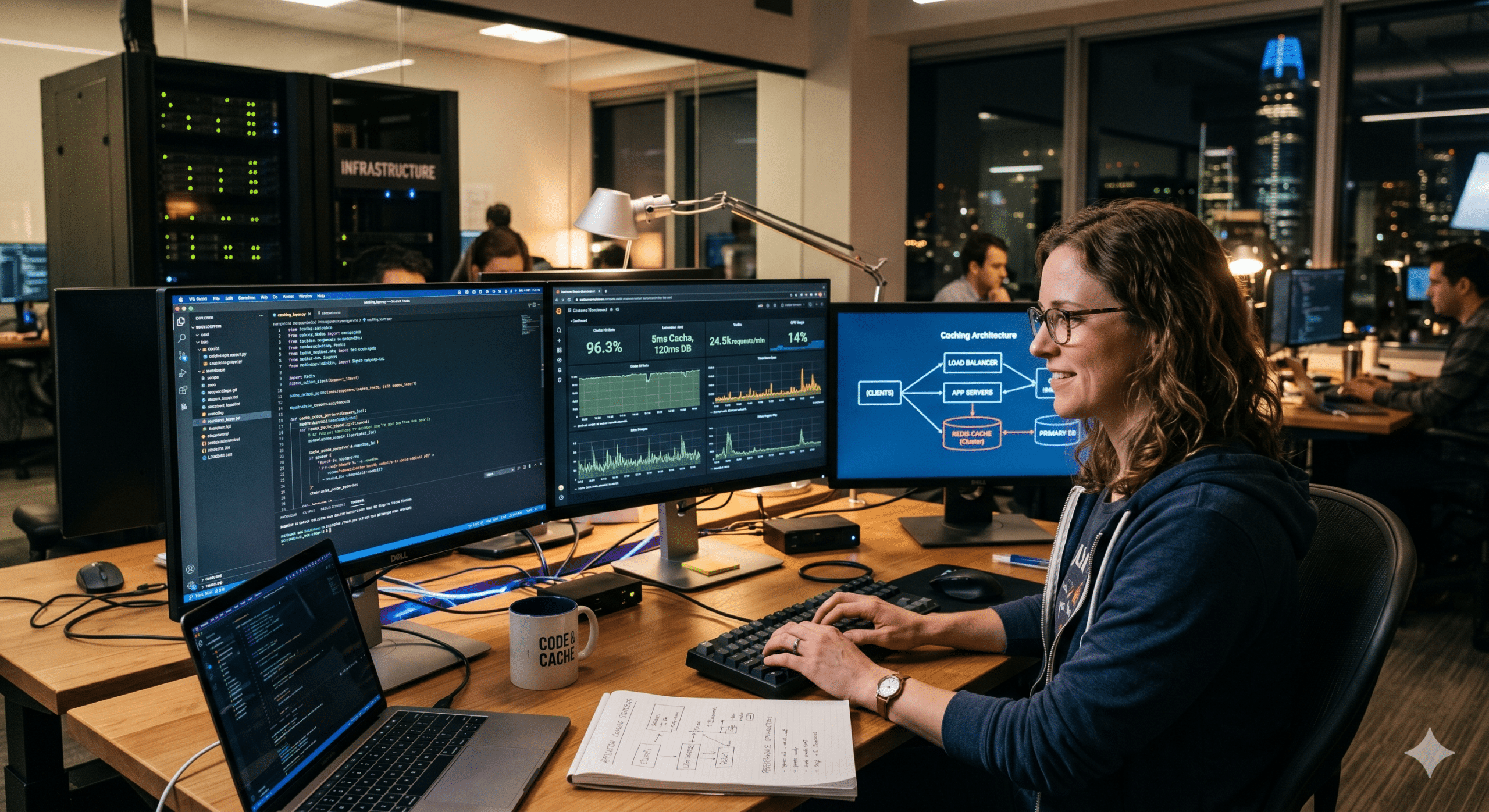
Application Caching Strategies: The Smart Performance Secret Behind Fast, Scalable, and Reliable Web Applications
In today’s digital world, speed is no longer considered a luxury. It has become an expectation. Whether someone is shopping online, browsing a news website, using a banking application, managing…
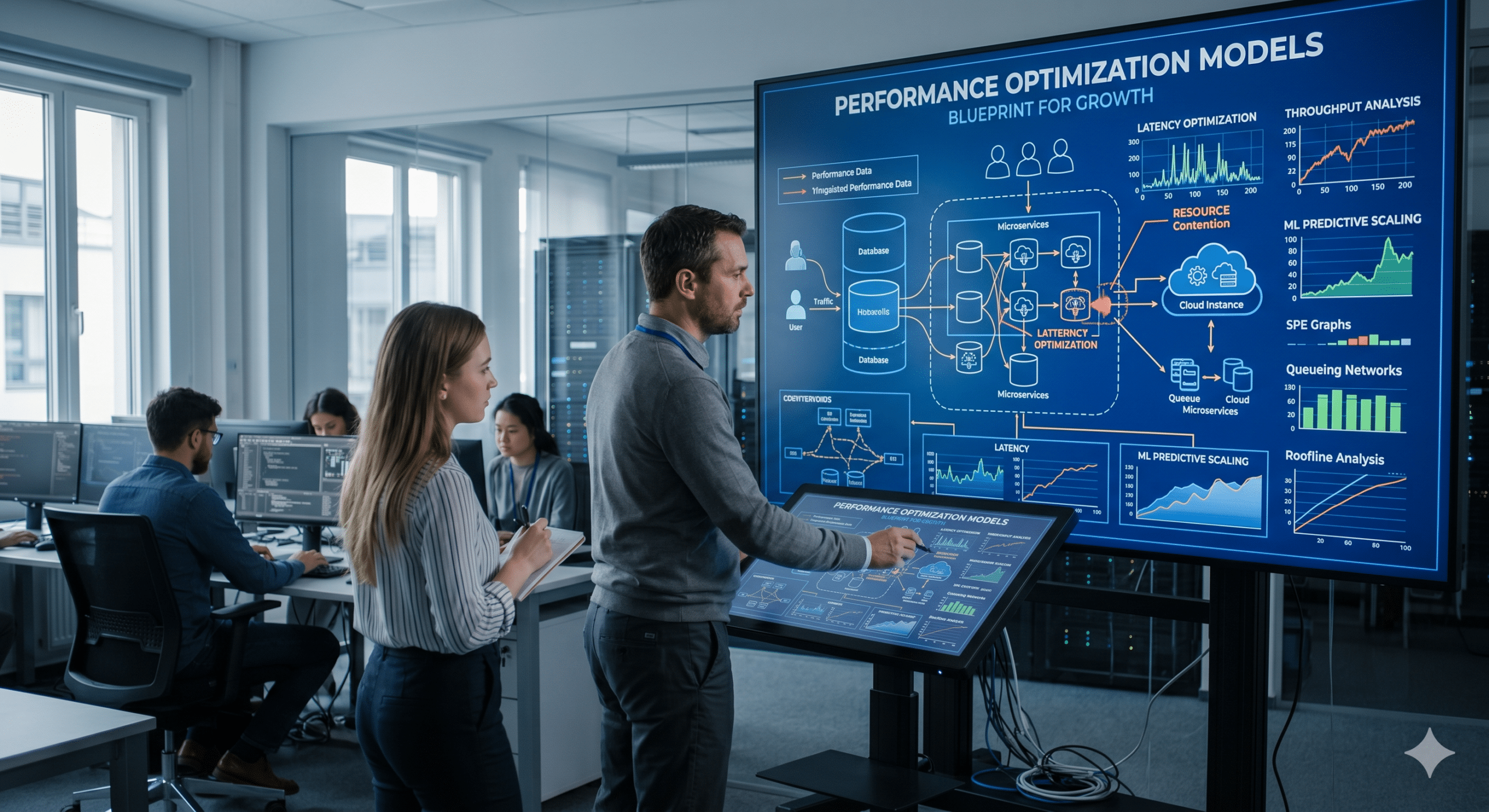
Performance Optimization Models: The Blueprint for Faster Systems, Smarter Operations, and Sustainable Business Growth
In today’s technology-driven world, organizations are constantly searching for ways to improve efficiency, reduce costs, and deliver better experiences to customers. Whether it is a website serving thousands of visitors…
Edge Computing Basics: The Technology Revolution Happening Closer Than You Think
In today’s digital world, speed matters more than ever. Whether you’re streaming a movie, using a navigation app, making an online purchase, monitoring industrial equipment, or connecting smart devices in…
API Gateways: The Digital Traffic Controllers Powering Modern Applications
In today’s connected world, software applications rarely operate in isolation. Whether you’re shopping online, booking a hotel room, transferring money through a banking app, ordering food for delivery, or streaming…
Serverless Architecture Fundamentals: The Smart Way Modern Businesses Build and Scale Applications
Technology has always evolved in cycles. First came massive on-premises data centers. Then cloud computing transformed the way businesses accessed computing resources. Today, another major shift is reshaping software development…
Application Layers Explained: The Invisible Technology Behind Everything You Do Online
Have you ever wondered what really happens when you open a website, send an email, watch a video on YouTube, or chat with someone on WhatsApp? Most people assume the…
Load Balancing Explained: The Hidden Technology That Keeps Modern Websites Fast and Online
Every time you visit a website, stream a movie, order food online, or join a video meeting, there’s a good chance a load balancer is working behind the scenes. Most…
Client-Server Model Breakdown: The Invisible Technology Behind Every Click, Stream, and Online Transaction
Client-Server Model Breakdown is one of the most important concepts in modern computing, yet most people use it every day without realizing it. Every time you visit a website, stream…